●Frame. Relay is simplified form. of (71) ,similar in principle to (72) ,in which synchronous,frames of data are routed to different destinations depending on header information.Packets are routed throught one or more Virtual Circuits known as (73) .Most
题目
●Frame. Relay is simplified form. of (71) ,similar in principle to (72) ,in which synchronous,frames of data are routed to different destinations depending on header information.
Packets are routed throught one or more Virtual Circuits known as (73) .Most Virtual Circuits are (74) ,which means that the network provider sets up all DLCI connections at subscription time. (75) are also part of the Frame. Relay specification.They privide a link that only lasts only as long as the session.
(71) A.Datagram Switching
B.Datagram Routing
C.Packet Switching
D.packet Routing
(72) A.X.21
B.X.25
C.X.28
D.X.29
(73) A.DLCIs
B.HDLCs
C.SDLCs
D.DLs
(74) A.Permanent Circuits
B.Permanent Virtual Circuits
C.Switched Virtual Circuits
D.Switching Circuits
(75) A.Permanent Circuits
B.Permanent Virtual Circuits
C.Switched Virtual Circuits
D.Switched Circuits
相似考题
参考答案和解析
【解析】帧中继是报文交换的一种简化形式,原理上与X.25类似。其是同步的,每一帧的数据都通过其包头信息路由到不同的目的地。
数据包通过被称之为DLCIs的一条或多条虚电路路由。大部分的虚电路是永久虚电路,也就是网络提供商在签署协议时就已经建立好了所有的DLCI连接。交换虚电路也是帧中继的一种规范,即提供商只在会话期间提供链路。
更多“●Frame. Relay is simplified form. of (71) ,similar in principle to (72) ,in which synchron ”相关问题
-
第1题:
Melissa and LoveLetter made use of the trust that exists between friends or colleagues. Imagine receiving an(71)from a friend who asks you to open it. This is what happens with Melissa and several other similar email(72). Upon running, such worms usually proceed to send themselves out to email addresses from the victim's address book, previous emails, web pages(73)As administrators seek to block dangerous email attachments through the recognition of well-known(74), virus writers use other extensions to circumvent such protection. Executable(.exe)files are renamed to .bat and .cmd plus a whole list of other extensions and will still nm and successfully infect target users.Frequently, hackers try to penetrate networks by sending an attachment that looks like a flash movie, which, while displaying some cute animation, simultaneously runs commands in the background to steal your passwords and give the(75)access to your network.
A.attachment
B.packet
C.datagram
D.message
正确答案:A
解析:Melissa和LoveLetter利用了朋友和同事之间的信任。设想你收到了一个附件,朋友要求你打开它。这就是Melissa和其他类似的电子邮件蠕虫危害的方式。一旦被运行,这种蠕虫常常就从受害人的地址簿、以前的电子邮件、Web页面缓存区等地方发现邮件地址,并且把它们发送出去。在管理人员通过识别众所周知的扩展名企图阻挡危险的email附件时,病毒的作者们则使用了其他的扩展名来破坏这种保护。可执行文件(.exe)被重新命名为.bat和.cmd,再加上其他的扩展名,而且仍然可以运行,成功地危害目标用户。黑客们经常试图穿透网络发送一种像是flash影像的附件,当这种flash演示引人入胜的动画时,同时就在后台运行命令来偷窃你的口令,给了那些解密高手访问你的网络的机会。 -
第2题:
71-72
第71题:
 正确答案:D
正确答案:D
-
第3题:
1、下列序列中哪个是最小堆?
A.2, 55, 52, 72, 28, 98, 71
B.2, 28, 71, 72, 55, 98, 52
C.2, 28, 52, 72, 55, 98, 71
D.28, 2, 71, 72, 55, 98, 52
2, 28, 52, 72, 55, 98, 71 -
第4题:
Mobile computers-which(71)laptops, notebooks, subnotebooks and handhelds-(72)so ubiquitous in such a short time, no surprise to hear who say: "It will define the leading edge(73)the next five years or so." The most remarkable(74)mobile computers is the amount of data storage and memory packed(75)their tiny boxes. These devices not only handle windows easily but also run storage-hungry programs.
A.included
B.include
C.have included
D.have become
E.had become
正确答案:B
-
第5题:
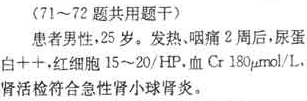
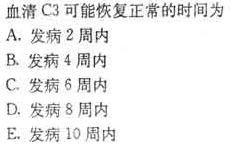
(71-72题共用题干)

第71题:
 正确答案:A
正确答案:A
-
第6题:
某试样硬度测定时的5个值分别是70、71、72、73、71,则其中值为。
A.70
B.71
C.72
D.73
71
