单选题An administrator is using a protocol analyzer to monitor traffic between two servers. However, the only traffic that appears is broadcast and traffic originating from the administrator's PC. Which of the following devices is the administrator plugged i
题目
Hub
Bridge
Switch
Router
相似考题
参考答案和解析
更多“单选题An administrator is using a protocol analyzer to monitor traffic between two servers. However, the only traffic that appears is broadcast and traffic originating from the administrator's PC. Which of the following devices is the administrator plugged i”相关问题
-
第1题:
An administrator is troubleshooting a communication issue between two computers on the sameLayer 2 switch.Which of the following is the BEST way to determine if the switch is causing the issue?()A. Setup an ACL that allows and logs all IP traffic between the two computers
B. Configure a spanning tree to check for a loop
C. Setup a span port on the switch to watch for CRC errors
D. Connect both computers using a crossover cable
参考答案:D
-
第2题:
Refer to the exhibit.The network administrator requires easy configuration options and minimal routing protocol traffic.Which two options provide adequate routing table information for traffic that passes between the two routers and satisfy the requests of the network administrator?()

A.a dynamic routing procotol on InternetRouter to advertise summarized routers to CentralRouter.
B.a dynamic routing procotol on CentralRouter to advertise summarized routers to InternetRouter.
C.a static route on InternetRouter to direct traffic that is destined for 172.16.0.0/16 to CentralRouter.
D.a dynamic routing procotol on InternetRouter to advertise all routes to CentralRouer.
E.a dynamic routing procotol on CentralRouer to advertise all routes to InternetRouter
F.a static,default route on CentralRouter that directs traffic to InternetRouter.
参考答案:C, F
-
第3题:
What are two reasons that a network administrator would use access lists (Choose two.)()。
- A、to control vty access into a router
- B、to control broadcast traffic through a router
- C、to filter traffic as it passes through a router
- D、to filter traffic that originates from the router
- E、to replace passwords as a line of defense against security incursions
正确答案:A,C -
第4题:
An administrator has purchased monitoring software that can be configured to alert administrators when hardware and applications are having issues. All devices are configured with SNMP, but the administrator wants to further secure the SNMP traffic. Which of the following settings would BEST provide additional monitoring security?()
- A、Setting up a custom community name
- B、Configuring the network to block traffic on port 161
- C、Configuring the Windows Firewall to block port 161
- D、Setting SNMP to read only on the devices
- E、Installing new MIBs
正确答案:D,E -
第5题:
An administrator is using a protocol analyzer to monitor traffic between two servers. However, the only traffic that appears is broadcast and traffic originating from the administrator's PC. Which of the following devices is the administrator plugged into? ()
- A、Hub
- B、Bridge
- C、Switch
- D、Router
正确答案:C -
第6题:
Which of the following technologies allows an administrator to submit traffic to an IDS for review?()
- A、Spanning tree
- B、VLAN
- C、PoE
- D、Port mirroring
正确答案:D -
第7题:
You are the network administrator for your company. A Windows Server 2003 computer named Router11 is used to connect the network to the Internet. You find out that some computers on the network are infected with a worm, which occasionally sends out traffic to various hosts on the Internet. This traffic always uses a certain source TCP port number.You need to identify which computers are infected with the worm. You need to configure a solution on Router11 that will perform the following two tasks: Detect and identify traffic that is sent by the worm. Immediately send a notification to a network administrator that the infected computer needs to be repaired. What should you do?()
- A、Configure a WMI event trigger.
- B、Configure a Network Monitor capture filter.
- C、Configure a Network Monitor trigger.
- D、Configure a System Monitor alert.
正确答案:C -
第8题:
多选题An administrator has purchased monitoring software that can be configured to alert administrators when hardware and applications are having issues. All devices are configured with SNMP, but the administrator wants to further secure the SNMP traffic. Which of the following settings would BEST provide additional monitoring security?()ASetting up a custom community name
BConfiguring the network to block traffic on port 161
CConfiguring the Windows Firewall to block port 161
DSetting SNMP to read only on the devices
EInstalling new MIBs
正确答案: D,E解析: 暂无解析 -
第9题:
单选题A network administrator wants to permit Telnet traffic initiated from the address book entry the10net in azone called UNTRUST to the address book entry Server in a zone called TRUST.However, the administrator does not want the server to be able to initiate any type of traffic from the TRUSTzone to the UNTRUST zone. Which configuration would correctly accomplish this task?()AA
BB
CC
DD
正确答案: B解析: 暂无解析 -
第10题:
单选题A system administrator is monitoring a system that has recently shown a decrease in performance. The administrator suspects there is an overload of traffic on a single Ethernet adapter. Which of the following commands is best to identify a possible overload of the Ethernet adapter?()Aping
Biostat
Cnetstat
Difconfig
正确答案: C解析: 暂无解析 -
第11题:
单选题An administrator is using a protocol analyzer to monitor traffic between two servers. However, the only traffic that appears is broadcast and traffic originating from the administrator's PC. Which of the following devices is the administrator plugged into? ()AHub
BBridge
CSwitch
DRouter
正确答案: D解析: 暂无解析 -
第12题:
单选题Which of the following technologies allows an administrator to submit traffic to an IDS for review?()ASpanning tree
BVLAN
CPoE
DPort mirroring
正确答案: B解析: 暂无解析 -
第13题:
The following exhibit displays the NetFlow statistics for a CIS router, which will be helpful for a network administrator to collect IP traffic information.Which two numbers separately refer to the percentage of packets sized between 32 and 64 bytes and the number of flows in progress?()
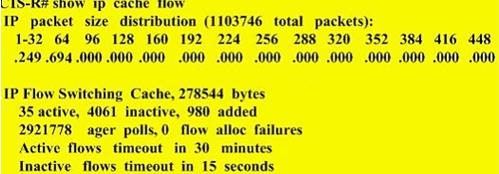
A. 24.9%, 980
B. 6.94%, 980
C. 69.4%, 35
D. cannot be determined from this output
E. 69.4%, 4061
参考答案:C
-
第14题:
What are two reasons that a network administrator would use access lists (Choose two.)()。A.to control vty access into a router
B.to control broadcast traffic through a router
C.to filter traffic as it passes through a router
D.to filter traffic that originates from the router
E.to replace passwords as a line of defense against security incursions
参考答案:A, C
-
第15题:
An administrator is troubleshooting a communication issue between two computers on the same Layer 2 switch. Which of the following is the BEST way to determine if the switch is causing the issue?()
- A、Setup an ACL that allows and logs all IP traffic between the two computers
- B、Configure a spanning tree to check for a loop
- C、Setup a span port on the switch to watch for CRC errors
- D、Connect both computers using a crossover cable
正确答案:D -
第16题:
A staff member reports that they cannot access the shared folder on the network; however, other staff members are reporting that they can access the shared folder. Which of the following is the BEST way to identify the problem?()
- A、The administrator should monitor all traffic between the staff member and the server.
- B、The administrator should reconfigure the RAID configuration to allow more space.
- C、The administrator should map a drive using the net use command.
- D、The administrator should allow the staff member to use a USB drive.
正确答案:C -
第17题:
An administrator is implementing a second server due to the increased usage. Which of the following optimization techniques is the administrator using?()
- A、Caching engines
- B、QoS
- C、Traffic shaping
- D、Load balancing
正确答案:D -
第18题:
Which of the following devices should an administrator connect to a protocol analyzer in order tocollect all of the traffic on a LAN segment?()
- A、Hub
- B、VLAN
- C、Router
- D、Server
正确答案:A -
第19题:
单选题The network administrator would like to generate synthetic traffic using the Service Assurance Agent contained in Cisco IOS. Which CiscoWorks network management application will be used to report the latency and availability for configured traffic operations on an end-to-end and hop-byhop (router-to-router) basis?()AnGenius Real-Time Monitor
BCiscoView
CDevice Fault Manager
DInternetwork Performance Monitor
正确答案: D解析: 暂无解析 -
第20题:
单选题Which of the following devices should an administrator connect to a protocol analyzer in order tocollect all of the traffic on a LAN segment?()AHub
BVLAN
CRouter
DServer
正确答案: A解析: 暂无解析 -
第21题:
单选题A staff member reports that they cannot access the shared folder on the network; however, other staff members are reporting that they can access the shared folder. Which of the following is the BEST way to identify the problem?()AThe administrator should monitor all traffic between the staff member and the server.
BThe administrator should reconfigure the RAID configuration to allow more space.
CThe administrator should map a drive using the net use command.
DThe administrator should allow the staff member to use a USB drive.
正确答案: D解析: 暂无解析 -
第22题:
单选题You are the network administrator for your company. A Windows Server 2003 computer named Router11 is used to connect the network to the Internet.You find out that some computers on the network are infected with a worm, which occasionally sends out traffic to various hosts on the Internet. This traffic always uses a certain source TCP port number.You need to identify which computers are infected with the worm. You need to configure a solution on Router11 that will perform the following two tasks: (1)Detect and identify traffic that is sent by the worm. (2)Immediately send a notification to a network administrator that the infected computer needs to be repaired. What should you do?()AConfigure a WMI event trigger.
BConfigure a Network Monitor capture filter.
CConfigure a Network Monitor trigger.
DConfigure a System Monitor alert.
正确答案: D解析: 暂无解析 -
第23题:
单选题An administrator is troubleshooting a communication issue between two computers on the same Layer 2 switch. Which of the following is the BEST way to determine if the switch is causing the issue?()ASetup an ACL that allows and logs all IP traffic between the two computers
BConfigure a spanning tree to check for a loop
CSetup a span port on the switch to watch for CRC errors
DConnect both computers using a crossover cable
正确答案: A解析: 暂无解析
