You want to enforce a Host Checker policy so that only users who pass the policy receive the Employee role. In the admin GUI, which two parameters must you configure?()A、Select "Require and Enforce" for the Host Checker Policy in the realm authentication
题目
You want to enforce a Host Checker policy so that only users who pass the policy receive the Employee role. In the admin GUI, which two parameters must you configure?()
- A、Select "Require and Enforce" for the Host Checker Policy in the realm authentication policy.
- B、Select "Evaluate Policies" for the Host Checker policy in the realm authentication policy.
- C、Configure the Host Checker policy as a role restriction for the Employee role.
- D、Configure the Host Checker policy as a resource access policy for the Employee role.
相似考题
更多“You want to enforce a Host Check”相关问题
-
第1题:
Your security policy requires that users authenticating to the Junos Pulse Access Control Service are connecting from a domain member endpoint on the internal corporate network.Which set of role access restrictions must you configure to enforce this security policy?()
A. Source IP and browser
B. Source IP and certificate
C. Certificate and Host Checker
D. Host Checker and source IP
参考答案:D
-
第2题:
Using vi, you want to save changes to the file myfile with :w!, but vi complains it cannot write to the file. Therefore, you want to check the write permissions on the file. To do this without leaving vi, you type:()
- A、 :!ls-I myfile
- B、 :/ls-l myfile
- C、 esc :Is -I myfile
- D、 :?ls-l myfile
正确答案:A -
第3题:
Your security policy requires that users authenticating to the Junos Pulse Access Control Service are connecting from a domain member endpoint on the internal corporate network.Which set of role access restrictions must you configure to enforce this security policy?()
- A、Source IP and browser
- B、Source IP and certificate
- C、Certificate and Host Checker
- D、Host Checker and source IP
正确答案:D -
第4题:
You are using the DBVERIFY utility to check the datafiles for any block corruption. You want to write the output of the dbv command to a file not to the screen. Which parameter of the DBVERIFY utility will you use?()
- A、 FILE
- B、 PARFILE
- C、 LOGFILE
- D、 FEEDBACK
正确答案:C -
第5题:
You want to check all the data blocks being written to the datafiles by analyzing the data on each block every time the DBWn process writes. Which action will you perform to check the data blocks?()
- A、 Set the value of the DB_BLOCK_CHECKING initialization parameter to TRUE
- B、 Use the ANALYZE utility.
- C、 Use the DBVERIFY utility.
- D、 Use the DBMS_REPAIR package.
正确答案:A -
第6题:
单选题You have created a Host Checker policy that contains multiple rules. You want to inform end users which rule specifically has failed.In the admin GUI, which configuration setting would you enable?()AEnable Custom Instructions
BPre-auth notification
CRemediation message
DSend reason strings
正确答案: B解析: 暂无解析 -
第7题:
多选题You want to enforce a Host Checker policy so that only users who pass the policy receive the Employee role. In the admin GUI, which two parameters must you configure?()ASelect Require and Enforce for the Host Checker Policy in the realm authentication policy.
BSelect Evaluate Policies for the Host Checker policy in the realm authentication policy.
CConfigure the Host Checker policy as a role restriction for the Employee role.
DConfigure the Host Checker policy as a resource access policy for the Employee role.
正确答案: B,D解析: 暂无解析 -
第8题:
单选题You have a Windows Server 2008 R2 Hyper-V server with a single network adapter that is connected to a virtual network. The virtual network is configured as External. Virtual machines (VMs) running on the server are not able to communicate with the host server over the network. You need to ensure that VMs running on the server are able to communicate with the host server over the network. In Virtual Network Manager,what should you do?()ASelect the Internal only connection type.
BSelect the Private virtual machine network connection type.
CSelect the Allow management operating system to share this network adapter check box.
DClear the Allow management operating system to share this network adapter check box.
正确答案: A解析: 暂无解析 -
第9题:
单选题You work as a database administrator for Supportcenter.cn. You determine that archiving was not successful in one of thedestinators. You want to check the alert log file for more information on this.Which initialization parameter gives you the location of the alert log file?()AUSER_DUMP_DEST
BCORE_DUMP_DEST
CALERT_LOG_DEST
DALERT_DUMP_DEST
ETRACE_DUMP_DEST
FBACKGROUND_DUMP_DEST
正确答案: D解析: 暂无解析 -
第10题:
单选题You create a virtual machine (VM) on a Windows Server 2008 R2 Hyper-V server. You plan to use this VM as the base image for new VMs. You need to ensure that you can import the base image multiple times on the original host server. In the Import Virtual Machine Wizard,which settings should you configure during each import process?()ASelect the Copy the virtual machine option and the Duplicate all files check box.
BSelect the Copy the virtual machine option. Clear the Duplicate all files check box.
CSelect the Move or restore the virtual machine option and the Duplicate all files check box.
DSelect the Move or restore the virtual machine option. Clear the Duplicate all files check box.
正确答案: B解析: 暂无解析 -
第11题:
单选题You want to perform the following operations for the DATA ASM disk group: -Verify the consistency of the disk. -Cross-check all the file extent maps and allocation tables for consistency. check whether the alias metadata directory and file directory are linked correctly. -Check that ASM metadata directories do not have unreachable allocated blocks. Which command accomplishes these tasks()?AALTER DISKGROUP data CHECK
BALTER DISKGROUP data CHECK DISK
CALTER DISKGROUP data CHECK FILE
DALTER DISKGROUP data CHECK DISK IN FAILURE GROUP 1
正确答案: B解析: 暂无解析 -
第12题:
多选题You want to remove the logoff option from your start menu. Which of the following options will allow you to enforce this setting? ()ALocal Policy
BGroup Policy
CRoaming Profile
DFrom the Display Applet in Control Panel
EFrom the accessibility applet in Control Panel
FOn the Advanced tab of the Taskbar/Start Menu dialog box, clear the Display logoff option.
正确答案: A,F解析: 暂无解析 -
第13题:
You are the administrator of the homeoffice.local domain. You want to create a shared printer for the company's executives so that they do not have to wait for their documents to print when the default printer's queue contains a large number of documents.
You configure the new high-priority printer and want to set permissions for the groups shown in the exhibit. Note: The default settings have been cleared.
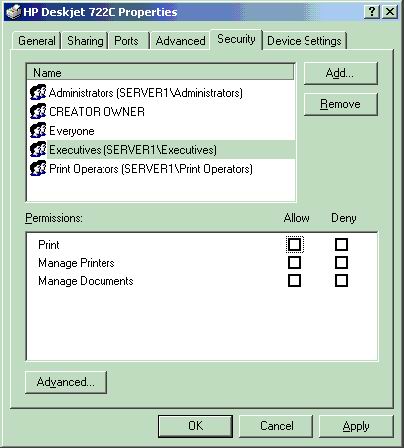
You select the check box to allow Print permission for the Executives group. You want only the Administrators, Print Operators, Server Operators, and Executives group to be able to print to the printer. What can you do? (Select all that apply).
A.Remove the Everyone group.
B.Select the check box to deny Print permission for the Everyone group.
C.Select the check box to deny Manage Documents permission for Everyone group.
D.Select all Deny check boxes for the Everyone group.
E.Clear all check boxes for Everyone group.
正确答案:AE
解析:Explanation: By default the Everyone group, to which all users are automatically added, has access to printer. Therefore, by removing the Everyone group, only the groups that have been explicitly been given permission to the printer would be able to use the printer. The same could be achieved by removing all permissions from the Everyone group.
Incorrect answers:
B: When a user has conflicting permissions to network resources as a result to his or her membership to one or more groups, the most restrictive permission is applied. However, a deny permission overrides all other permissions. All users are automatically added to the Everyone group therefore the deny print permission applied to the Everyone group will be inherited by all users and would override their other permissions to the printer. All users would then not be able to print.
C: When a user has conflicting permissions to network resources as a result to his or her membership to one or more groups, the most restrictive permission is applied. However, a deny permission overrides all other permissions. All users are automatically added to the Everyone group therefore the deny manage documents permission applied to the Everyone group will be inherited by all users and would override their other manage documents permissions to the printer. This will however not prevent all users from be able to use the printer.
D: When a user has conflicting permissions to network resources as a result to his or her membership to one or more groups, the most restrictive permission is applied. However, a deny permission overrides all other permissions. All users are automatically added to the Everyone group therefore the deny permissions are applied to the Everyone group will be inherited by all users and would override their other permissions to the printer. All users would then not have access to the printer.
-
第14题:
You want to check the EMP table in the user, Scott’s schema for block corruption. You also want to fix the corrupted blocks, if any. How will you accomplish the required task?()
- A、by using the ANALYZE utility
- B、by using the DBVERIFY utility
- C、by using the DB_BLOCK_CHECKING parameter
- D、by using the DBMS_REPAIR package
正确答案:D -
第15题:
You want to restrict access to a role based on the client machine from which the user is accessing the network.Which two role restrictions accomplish this goal? ()
- A、user name
- B、password length
- C、certificate
- D、Host Checker
正确答案:C,D -
第16题:
You want to perform the following operations for the DATA ASM disk group: -Verify the consistency of the disk. -Cross-check all the file extent maps and allocation tables for consistency. check whether the alias metadata directory and file directory are linked correctly. -Check that ASM metadata directories do not have unreachable allocated blocks. Which command accomplishes these tasks()?
- A、 ALTER DISKGROUP data CHECK
- B、 ALTER DISKGROUP data CHECK DISK
- C、 ALTER DISKGROUP data CHECK FILE
- D、 ALTER DISKGROUP data CHECK DISK IN FAILURE GROUP 1
正确答案:A -
第17题:
Your company has an Active Directory Domain Services (AD DS) domain. You are installing the RD Session Host (RD Session Host) role service in Server Manager on a server that runs Windows Server 2008 R2. The Audio and video playback check box on the Configure Client Experience page is not available. You need to ensure that you can enable audio and video playback for users connecting to the RD Session Host server. Which two actions should you perform?()
- A、Start the Windows Audio service.
- B、Install the Desktop Experience feature.
- C、Install Connection Manager Administration Kit feature.
- D、Start the Windows Audio EndPoint Builder service.
正确答案:A,B -
第18题:
单选题一 Good morning. ,- Good morning! I need a check to send to my publisher in New York.()AWhat can I do for you, Madam
BWhat do you want to buy, Madam
CWhy do you come here, Madam
正确答案: A解析: 暂无解析 -
第19题:
单选题You are creating a view to join the Customers and Orders tables in a SQL Server 2005 database. You need to ensure that the view cannot be affected by modifications to underlying table schemas. You want to accomplish this goal by using the least possible amount of overhead. What should you do?()ACreate CHECK constraints on the tables.
BCreate a DDL trigger to roll back any changes to the tables if the changes affect the columns in the view.
CCreate the view, specifying the WITH SCHEMABINDING option.
DCreate the view, specifying the WITH CHECK option.
正确答案: A解析: 暂无解析 -
第20题:
单选题You want to provide all users in your corporation with a single agent that provides access to multiple connection types conditionally. For example, you connect to the Junos Pulse Access Control Service if you are connected to the intranet, but you connect to the Junos Pulse Secure Access Service if you are on a remote network. Which agent should you use for this type of connection requirement?()AJunos Pulse should be configured with location awareness rules configured.
BOdyssey Access Client should be installed with Host Checker configured to check the client's location.
CJunos Pulse should be configured with all components installed.
DAgentless access should be enabled so that clients can connect to any service without concern for installing an agent.
正确答案: A解析: 暂无解析 -
第21题:
单选题Using vi, you want to save changes to the file myfile with :w!, but vi complains it cannot write to the file. Therefore, you want to check the write permissions on the file. To do this without leaving vi, you type:()A:!ls-I myfile
B:/ls-l myfile
Cesc :Is -I myfile
D:?ls-l myfile
正确答案: B解析: 暂无解析 -
第22题:
单选题You are a technician at TestKing. Your assistant applied an IP access control list to Router TK1. You want to check the placement and direction of the access control list.Which command should you use?()Ashow access-list
Bshow ip access-list
Cshow ip interface
Dshow interface
Eshow interface list
正确答案: C解析: 暂无解析 -
第23题:
多选题You work as a database administrator for Supportcenter.cn. You want to administer your database servers, which are running on different host machines, using the Web-enabled grid control interface. You have configured the agent on the host machines. You have started the Oracle Database 10g Grid Control utility on your machine. Which two additional components would you configure to achieve this objective?()AApplication Server Control
BOracle Management Service
COracle Enterprise Manager Repository
DOracle Enterprise Manager Database Control
正确答案: A,D解析: 暂无解析 -
第24题:
单选题You want to check all the data blocks being written to the datafiles by analyzing the data on each block every time the DBWn process writes. Which action will you perform to check the data blocks?()ASet the value of the DB_BLOCK_CHECKING initialization parameter to TRUE
BUse the ANALYZE utility.
CUse the DBVERIFY utility.
DUse the DBMS_REPAIR package.
正确答案: A解析: 暂无解析
